AWS has introduced Amazon Bedrock AgentCore Payments, built with Coinbase and Stripe.
That sounds like a payment feature. It is really a sign that AI agents are moving into a more consequential phase: they are not only reading documents, calling tools, and operating cloud resources. They are beginning to participate in transactions.
The moment an agent can pay for a service, unlock a paid MCP resource, buy a digital good, or trigger a payment workflow, the risk model changes. The question is no longer only, “Can the agent use this tool?” The better question is:
Under what identity, budget, approval policy, and audit trail can this agent spend money?
This is the same pattern we covered in AWS MCP Server Is GA: Why Cloud Agent Access Needs a Real Control Plane. Tool access needs governance. Payment access needs even stricter governance because mistakes create real financial exposure.
TL;DR
- Amazon Bedrock AgentCore Payments gives agent builders a way to integrate payment flows into agentic applications.
- AWS says the launch is built with Coinbase and Stripe, and includes support for paid resources such as paid MCP tools and services.
- The important shift is not “AI can pay.” The important shift is that agents need budget policy, payment identity, approval checkpoints, logs, and revocation paths.
- Builders should treat agent payments like production financial operations, not like another API call.
- Start with low-value, narrow-scope transactions before allowing recurring, high-value, or production-critical payments.
What AWS announced
AWS describes AgentCore Payments as part of Amazon Bedrock AgentCore, aimed at agents that need to transact with third-party services. The launch post frames the feature around a practical problem: many useful agent workflows eventually need to access paid resources, pay for services, or complete a transaction on behalf of a user or business.
The announcement highlights Coinbase and Stripe as launch collaborators. It also connects the feature to paid MCP resources, which matters because MCP is becoming a common way for agents to discover and use tools.
In plain language, the stack looks like this:
- an agent identifies that a task requires a paid resource
- the resource or service requests payment
- the agent application routes the payment through a controlled payment flow
- the payment provider handles the transaction mechanics
- the system returns proof or authorization so the agent can continue
That can be useful. It can also be dangerous if teams wire it up without policy.
Why this matters now
Agent systems have been expanding in layers.
First, they could chat.
Then, they could call tools.
Then, they could browse websites, execute code, use MCP servers, and operate infrastructure.
Now, some agents are moving toward economic action.
That is a different category of capability. A wrong search query wastes tokens. A wrong infrastructure action can break a system. A wrong payment can spend money, buy the wrong resource, trigger a refund workflow, violate procurement rules, or create accounting noise that a human has to untangle.
For consumer apps, the issue is user consent. For companies, the issue is spend governance. For developers, the issue is safe defaults.
If agent payments become common, teams will need patterns that feel more like cloud IAM, expense policy, procurement controls, and security review than ordinary checkout UX.
The payment-control flow
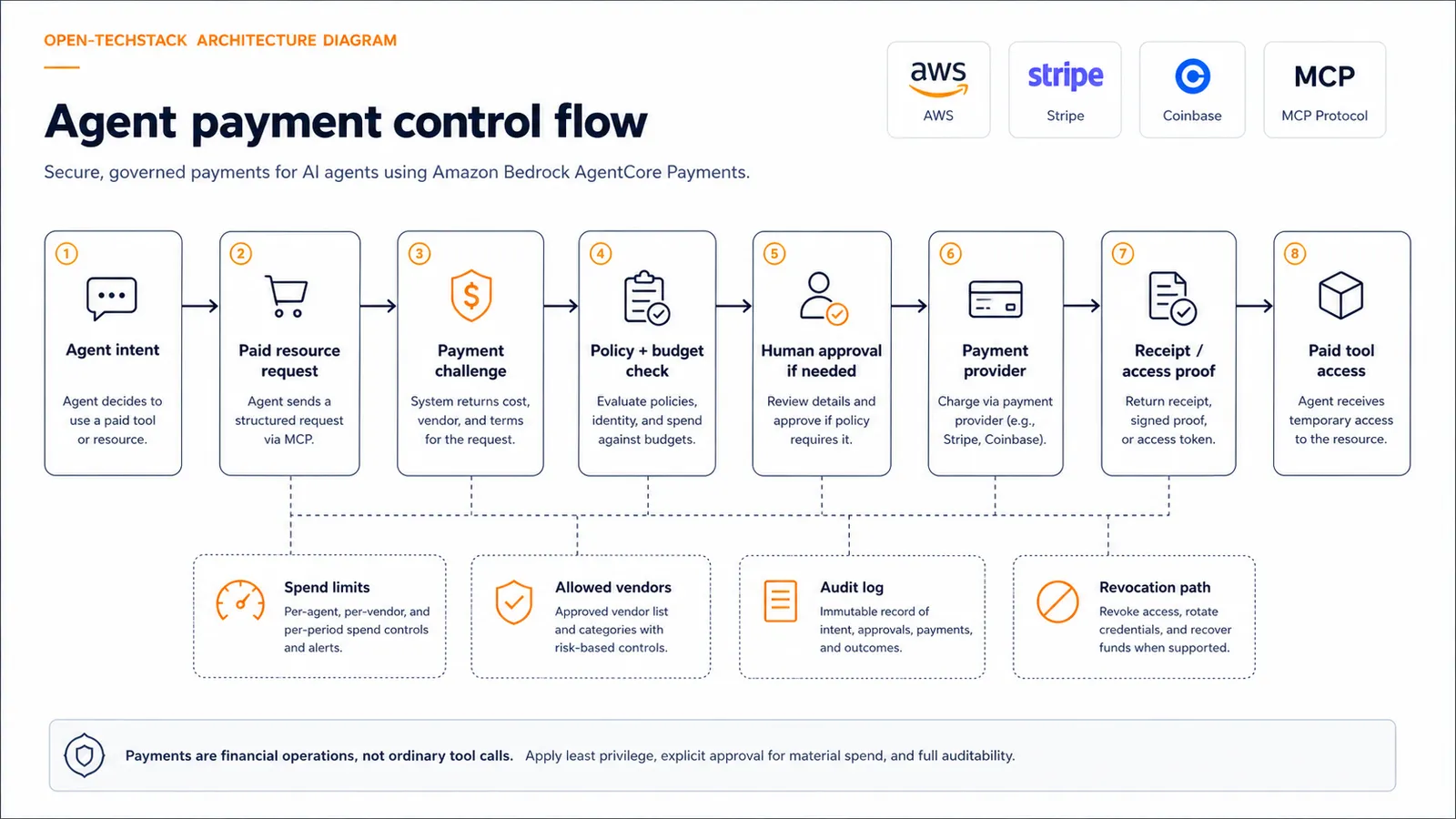
The safest mental model is not “the agent pays.” It is:
agent intent -> paid resource request -> payment challenge
-> policy check -> user or admin approval
-> payment provider -> receipt or proof
-> resource access
-> audit logThat middle layer is the product. Without it, payment-enabled agents become too easy to misuse.
What should be governed
Agent payments need more than a card on file.
1. Payment identity
Who is paying?
It may be a user, a workspace, a department, a service account, or a company billing profile. Those are not interchangeable. A personal productivity agent buying a $5 report is not the same as an enterprise support agent purchasing data access for a customer case.
Payment identity should be explicit in logs and policy.
2. Spending scope
Agents should not receive a vague instruction like “buy what you need.” They need bounded spend rules:
- maximum amount per transaction
- maximum amount per day or billing period
- allowed vendors or resource types
- blocked categories
- currency and region constraints
- approval thresholds
This is boring, which is exactly why it matters.
3. Human approval
Not every payment needs a human in the loop. But some definitely do.
Low-risk payments can be automated when the resource is known, the amount is small, and the user has already opted in. Higher-risk payments should pause for approval.
Good approval prompts should show:
- what the agent wants to buy
- why it says the purchase is needed
- the vendor or endpoint
- the amount
- whether it is one-time or recurring
- what happens after approval
That is much more useful than a generic “Allow payment?” modal.
4. Receipts and audit logs
Every agent payment should leave a trail.
At minimum, log:
- agent identity
- user or workspace identity
- payment provider
- vendor or paid resource
- requested amount
- approved amount
- approval actor
- receipt or payment proof reference
- task context
- success or failure state
If the agent later claims “I needed this to finish the task,” the system should be able to reconstruct what happened.
5. Revocation and refunds
Payment governance is incomplete if the only control is pre-approval.
Teams also need after-the-fact controls:
- revoke access to a paid tool
- cancel recurring authorization
- dispute or refund a charge
- disable a payment profile
- block a vendor
- suspend an agent role
Agents will make mistakes. A good system assumes that and makes cleanup possible.
Decision matrix: when should agents be allowed to pay?
| Payment scenario | Starting posture |
|---|---|
| Free resource discovery | Allow normally |
| Low-cost one-time paid resource | Allow with budget cap and clear user consent |
| Paid MCP tool call | Allow only with tool allowlist and logs |
| Recurring subscription | Require explicit human approval |
| High-value transaction | Require human approval and policy review |
| Vendor not previously approved | Block or route to admin approval |
| Production-critical purchase | Require procurement or owner approval |
The rule is simple: the more durable, expensive, or operationally important the purchase is, the less autonomy the agent should have.
Common mistakes
Treating payment as just another tool call
Payments are not normal tool calls. A payment changes financial state. It may also create legal, tax, procurement, refund, or customer-support obligations.
Hiding the vendor behind the agent
The user should know who is being paid. A trusted agent interface should not obscure the actual merchant, service, or MCP resource.
Skipping budget limits
Even if every payment is individually small, repeated small payments can add up. Budget windows are a basic safety layer.
Forgetting recurring authorization
One-time approval and recurring approval are different. If an agent can initiate recurring access, the user needs a clear way to see and revoke it.
Logging only the payment provider event
Payment-provider logs are not enough. The agent system also needs task-level context: what the agent was trying to do, what policy it matched, and who approved it.
Who should pay attention
This launch matters for:
- AI agent platform builders
- SaaS teams exposing paid MCP tools
- developer-tool companies building paid agent workflows
- fintech and commerce teams experimenting with AI assistants
- enterprise teams evaluating autonomous procurement or operations agents
- security teams thinking about agent permissions
It matters less if your agents only read internal documents or operate inside a fixed, non-commercial workflow.
The bigger pattern
Agent payments are part of a broader trend: AI systems are gaining access to more consequential surfaces.
Browser agents interact with websites. Coding agents touch repositories. Cloud agents inspect infrastructure. MCP servers expose internal tools. Payment-enabled agents can spend money.
Each step makes agents more useful. Each step also makes governance more important.
This is why the best agent systems will not be the ones with the most autonomy. They will be the ones with the clearest boundaries: identity, policy, logs, budgets, approvals, and recovery paths.
If you want the security side of the same argument, read AI Agent Browser Security Checklist: Let Agents Use Your Site Without Letting Bots Abuse It and AI Coding Agents Need Guardrails, Not More Autonomy.
FAQ
Does AgentCore Payments mean agents can buy anything?
No. It gives builders a payment integration path. What an agent can buy still depends on the application, payment provider, resource, user consent, and policy layer around the agent.
Is this only about cryptocurrency?
No. Coinbase is part of the launch story, but Stripe is also involved, and the broader pattern is payment-enabled agent workflows, not only crypto payments.
Should agents be allowed to make purchases without asking?
Only in narrow, low-risk cases where the user or organization has already defined clear limits. Anything recurring, expensive, unusual, or production-impacting should require approval.
How should paid MCP tools be handled?
Treat paid MCP access like any other sensitive tool: allowlist the server, set spend caps, log every paid call, show the user what is being purchased, and require approval above a threshold.
Bottom line
Agent payments are useful, but they move AI agents into financial operations.
That means builders need to design for more than checkout success. They need budget policy, consent, approval, receipts, audit logs, and revocation.
If your agent can spend money, it should also be able to explain why, show who approved it, prove what was purchased, and stop when the policy says stop.
Related posts
- AWS MCP Server Is GA: Why Cloud Agent Access Needs a Real Control Plane
- AI Agent Browser Security Checklist: Let Agents Use Your Site Without Letting Bots Abuse It
- AI Coding Agents Need Guardrails, Not More Autonomy
- Why MCP Is Becoming the Default Standard for AI Tools in 2026
- How Teams Use MCP Servers for Real Internal Tooling
